What Is Two-Factor Authentication? Why It Matters and How to Choose
NIST classifies SMS 2FA as restricted. CISA recommends FIDO2 as the only widely available phishing-resistant option. NCSC says passkeys should be consumers' first choice. The honest 2026 map of authentication tiers.
This is an informational summary of two-factor authentication (2FA) drawn from NIST, CISA, NCSC, IETF, W3C, FIDO Alliance, and major vendor security publications. It is not security advice or product recommendation. Authentication-tier comparisons are functional, not endorsements; no specific 2FA method or product is designated "best." Individual situations vary by service support, threat model, and accessibility needs. For high-stakes decisions consult a qualified security professional.
In 2017, Google began requiring its 85,000+ employees to use a hardware security key for sign-in, replacing Google Authenticator. About a year and a half later, in a July 2018 interview with Brian Krebs, a Google spokesperson summarized the result in one sentence — "We have had no reported or confirmed account takeovers since implementing security keys at Google." Around the same time, Microsoft's identity team reported that, based on their telemetry, accounts were over 99.9% less likely to be compromised when MFA was enabled (a figure most useful for credential-driven automated attacks rather than every threat). And Google's own 2019 analysis of 350,000 hijacking attempts gave a tiered effectiveness picture — SMS codes blocked 100% of automated bots, 96% of bulk phishing, but only 76% of targeted phishing; on-device prompts blocked 100%, 99%, and 90% respectively; and security keys, in the underlying academic study, blocked 100% across all three. So what is two-factor authentication, and should you use it?
The short answer. Two-factor authentication (2FA) means combining two authentication elements from different categories — something you know (password, PIN), something you have (phone, security key), or something you are (fingerprint, face). Two passwords are not 2FA, because they are the same category. The published guidance is consistent across four authoritative bodies — NIST's SP 800-63B-4 (finalized July 31, 2025) classifies SMS-based one-time passwords as a "restricted authenticator," CISA recommends FIDO/WebAuthn as the only widely available phishing-resistant MFA, and the UK's NCSC announced on April 23, 2026 that passkeys should now be consumers' first choice of login. The hierarchy of strength runs SMS < TOTP < FIDO2 hardware key / passkey, with FIDO2's domain-binding making it structurally phishing-resistant. The rest of this post walks through what each tier actually does, the effectiveness numbers behind the headlines, and the bypass techniques that 2FA does not, on its own, prevent.
This post walks through seven things — (1) what 2FA actually is in plain terms, (2) how TOTP authenticator apps work, (3) why SMS 2FA has been progressively downgraded by standards bodies, (4) the FIDO2 / WebAuthn / passkey phishing-resistant tier and what makes it different, (5) the effectiveness data and what each cited number actually means, (6) honest 2FA bypass techniques (MFA fatigue, AitM proxies, session theft), and (7) a comparison of authentication tiers plus the long-term direction toward passkeys.
What is two-factor authentication, in plain terms
Authentication factors are commonly grouped into three categories — a framing that runs through NIST guidance, the CISA "More Than a Password" hub, and most identity-provider documentation:
- Something you know (knowledge factor): password, PIN, the answer to a security question
- Something you have (possession factor): phone, hardware security key, smart card, OTP token
- Something you are (inherence factor): fingerprint, face, iris, voice
Two-factor authentication requires two different categories from the list. Two passwords are still one category, so they are not 2FA. Password plus an SMS code is knowledge plus possession, which qualifies. Password plus Touch ID is knowledge plus inherence, which also qualifies. Multi-factor authentication (MFA) is the broader umbrella term for "two or more factors"; in practical guidance "2FA" and "MFA" are often used interchangeably for the consumer scenario.
The history of 2FA in commercial use begins with RSA Security's SecurID hardware token (1986), which displayed a new code every 60 seconds based on an internal clock and a factory-encoded seed. Mobile authenticator apps based on the IETF TOTP standard (RFC 6238, May 2011) made software-based one-time codes practical at scale — Google Authenticator launched in 2010 in the same spirit. The FIDO2 standard combines two parts — the W3C WebAuthn specification (Candidate Recommendation in April 2018, full W3C Recommendation on March 4, 2019) and the FIDO Alliance's Client to Authenticator Protocol v2 (CTAP2). On May 5, 2022, Apple, Google, and Microsoft jointly announced expanded support for "passkeys," WebAuthn credentials that can be synced across a user's devices via cloud (Apple's iCloud Keychain, Google Password Manager, Microsoft Authenticator), making FIDO2's security model usable without a physical hardware key.
How TOTP authenticator apps work (RFC 6238)
TOTP — Time-based One-Time Password — is defined by IETF RFC 6238, published in May 2011 as an extension of the earlier HOTP standard (RFC 4226, which uses an event counter rather than time). The mechanism is straightforward and self-contained:
- At enrollment, the user and service share a secret (typically a base32-encoded string), often via a QR code scan
- The user's authenticator app and the service's server each combine that shared secret with the current Unix time, run HMAC-SHA1, and produce a 6-digit code
- The default time window is 30 seconds — both sides recompute every 30 seconds
- The code is never transmitted across the network beforehand; both sides compute the same answer independently
This makes TOTP attractive for several reasons. It does not depend on the cellular network the way SMS does. It blocks credential stuffing and password spray attacks essentially completely — an attacker who has the password but not the live code cannot proceed. And it works offline, making it usable on any device that can hold the shared secret.
The weakness is that the user is the weak link. If a user is tricked into entering their TOTP code on a fraudulent site, the attacker forwards both the password and the code to the real service in real time. TOTP is not phishing-resistant in the formal sense — the FIDO Alliance, NIST, and CISA all draw this line clearly. The next sections explain what is. Common authenticator apps that implement RFC 6238 include Google Authenticator, Microsoft Authenticator, Authy, 1Password, Bitwarden, and Aegis.
Why SMS 2FA has been progressively downgraded by standards bodies
NIST's position on SMS 2FA has shifted over the years. The July 2016 public draft of SP 800-63B (Rev 3) explicitly proposed deprecating SMS-based one-time passcodes — a notable announcement in the security industry at the time. The final version softened the language and classified SMS as a "restricted authenticator" — usable, but with required mitigations and risk acknowledgements. The current finalized guidance, NIST SP 800-63B-4, published July 31, 2025, formally retains this restricted-authenticator classification for SMS and PSTN one-time passwords, and requires verifiers to acknowledge specific risks including SIM swap, number porting, device theft, and SS7-style man-in-the-middle attacks.
The two underlying reasons SMS is weak:
SS7 protocol weakness. Signaling System 7 is the inter-carrier signaling protocol designed in the 1970s, and its messages were not designed with cryptographic authentication. An attacker with access to an SS7 gateway — through black-market access, a corrupted carrier insider, or some smaller carriers — can use Mobile Application Part messages such as UpdateLocation to intercept or redirect SMS messages destined for a target. A widely reported 2017 incident in Germany involved attackers exploiting SS7 access to intercept SMS-based bank-account 2FA codes, enabling unauthorized withdrawals from O2-Telefonica subscribers.
SIM swap (SIM hijacking). The attack uses social engineering to convince a carrier customer-service agent to port the victim's number to a SIM controlled by the attacker. Once the swap completes, all SMS messages including 2FA codes go to the attacker. The August 2019 hijacking of Twitter CEO Jack Dorsey's account is the most famous example — for roughly 20 minutes, racist and bomb-threat tweets appeared on his timeline. Twitter publicly attributed the incident to a "security oversight" by Dorsey's wireless carrier rather than a Twitter platform compromise.
SMS is still widely deployed despite these weaknesses for legitimate reasons — it requires no app installation, has the lowest accessibility barrier, and even a weak second factor is dramatically better than none against automated credential attacks. Microsoft's commonly cited "99.9 percent of account compromise attacks" figure (Melanie Maynes, August 2019) was reported in the context of any MFA, including SMS, against the categories of attack Microsoft observed at scale — primarily automated. SMS 2FA is meaningfully better than password-only; it is just not the strongest tier available.
FIDO2 / WebAuthn / passkeys — what makes them phishing-resistant
FIDO2 combines two specifications. The W3C WebAuthn API (full Recommendation since March 4, 2019) defines how websites in a browser request authentication from an external authenticator. The FIDO Alliance's CTAP2 protocol defines how the browser or operating system communicates with that authenticator over USB, NFC, or Bluetooth Low Energy. Together they implement a public-key cryptography model — the authenticator generates a key pair per registered website, registers the public key with the service, and proves possession of the private key during sign-in by signing a server-issued challenge. The private key never leaves the authenticator.
What makes this phishing-resistant is domain binding. The authenticator records which exact origin (scheme + host + port) it created each key pair for. When the user visits a fraudulent site at a similar-looking domain, the authenticator simply does not have a matching key — the site cannot lure it into producing a signature that the legitimate site would accept. Unlike a password or a TOTP code, there is no human-visible secret that can be copy-pasted into a phishing page; the cryptographic challenge-response happens entirely between the authenticator and the verified domain. Real-time phishing proxies that successfully bypass TOTP and SMS (the next section covers them) cannot bypass FIDO2 for this reason.
Authenticator types in the FIDO2 ecosystem:
| Type | Examples |
|---|---|
| Hardware security keys | YubiKey (Yubico), Google Titan, Feitian, SoloKey |
| Platform authenticators | Windows Hello, Apple Touch ID / Face ID, Android biometric |
| Passkeys (synced WebAuthn credentials) | Apple iCloud Keychain, Google Password Manager, Microsoft Authenticator, 1Password, Bitwarden |
Important honest caveat. FIDO2's phishing-resistance is at the design level. If the user's device is compromised by malware, the attacker can capture session cookies after a successful authentication — at which point the authentication itself is no longer the protective layer. Passkey cloud sync also adds a new attack surface: if the iCloud or Google account is compromised, the synced passkeys travel with it. Endpoint hygiene (OS and browser updates, restricted untrusted apps) and a strong account password on the cloud sync provider both matter. FIDO2 closes the largest remaining 2FA gap (real-time phishing) but does not eliminate every threat. For password-side defense-in-depth see the companion guide on whether password managers are safe.
Effectiveness data — what each cited number actually means
Several frequently cited statistics drive the 2FA conversation. Their precise meaning matters more than the headline.
Google's 2019 study of 350,000 hijacking attempts (Google Security Blog, May 2019) is the most useful single dataset for tier comparison. Tier-by-tier blocking against the three attack categories the study tracked:
- SMS code: 100% of automated bots, 96% of bulk phishing, 76% of targeted phishing
- On-device prompt: 100% of automated bots, 99% of bulk phishing, 90% of targeted phishing
- Security key: 100% across all three categories, per the underlying academic paper
The headline takeaway is the targeted column. Against a sophisticated attacker who has chosen a specific victim — the threat model that drives most consequential breaches — 76% (SMS) is meaningfully different from 90% (on-device prompt), and both are different from 100% (hardware security key). At population scale even 76% is enormously valuable, but for users whose threat model includes targeted attempts, the gap is what motivates upgrading.
Google's "no account takeovers since implementing security keys" (Krebs on Security, July 2018) is qualitative but powerful. Google deployed hardware security keys to its 85,000+ employees in early 2017, replacing Google Authenticator as the second factor. The reported result more than a year later — no successful account takeovers — is consistent with the 100% targeted-phishing block rate from the 2019 study. The data point has not been publicly contradicted in the years since.
Microsoft's "99.9% of account compromise attacks" (Melanie Maynes, August 2019; Alex Weinert in companion materials) is the most commonly quoted MFA figure. The published claim is that "MFA can block over 99.9 percent of account compromise attacks." The framing in the source does not narrow the claim to automated attacks specifically, but the empirical context supports interpreting it primarily as protection against credential-driven automated attacks (credential stuffing, password spray, basic phishing). For sophisticated targeted AitM attacks or social-engineering pathways, the same percentage does not apply — bypass cases like the 2022 Uber MFA-fatigue incident demonstrate that MFA is not a categorical guarantee.
Verizon's 2025 Data Breach Investigations Report reports that stolen credentials were the initial access vector in 22% of analyzed breaches; that stolen credentials accounted for 88% of basic web application attacks; and that 54% of ransomware victims had credentials previously exposed in infostealer logs. These are not direct measurements of MFA effectiveness, but they describe the scale of the credential-driven attack surface that 2FA exists to close.
2FA bypass techniques — honest threat enumeration
"Just turn on MFA" is good advice but a dangerous oversimplification. Several documented bypass techniques work against weaker tiers — and one (FIDO2) is structurally resistant to most of them.
MFA fatigue / push bombing. An attacker who already has the password repeatedly attempts to sign in, generating a stream of MFA push notifications on the user's phone. The user, annoyed or confused, eventually approves one — often after the attacker pretends to be IT support over a side channel. The September 2022 Uber breach is the most-discussed example. According to Uber's incident statement, an 18-year-old Lapsus$ group attacker repeatedly sent MFA approval requests to a contractor's phone for roughly an hour, then contacted them on WhatsApp posing as Uber IT support and convinced them to approve one request. Mitigations include "number matching" MFA (the user must read a number from the sign-in screen and enter it on their phone) and rate-limiting push notifications.
Real-time phishing proxies (Adversary-in-the-Middle). Open-source frameworks like evilginx2 and Modlishka, and commercial successors like EvilProxy, set up a fraudulent site that proxies traffic to the legitimate one in real time. The user enters their credentials and TOTP code, the proxy forwards them to the real service, and the proxy captures the session cookie returned after successful authentication. TOTP and SMS are both vulnerable; FIDO2 is structurally not, because the authenticator refuses to sign for the wrong domain — this is the single biggest reason the phishing-resistant tier matters.
Session token theft / cookie hijacking. Infostealer malware on the user's device extracts authenticated session cookies directly from the browser, bypassing the authentication step entirely. The Verizon DBIR 2025 finding that 54% of ransomware victims had credentials previously exposed via infostealers reflects how widespread this category has become.
OAuth consent phishing. The attacker sends a victim a link that requests OAuth permission to access the victim's Google or Microsoft account. The user authorizes the request without realizing they are granting a hostile application persistent access — and 2FA is not invoked because the user's identity provider has already authenticated them in their normal session.
Account-recovery flow abuse. Even if 2FA is strong, a weak recovery procedure (SMS-based fallback, easily-guessed security questions, social engineering of customer support) can bypass it. CISA and NCSC both consistently note that recovery procedures should be at least as strong as the primary authentication.
CISA puts the framing directly: "MFA bypass attacks are not theoretical risks but are happening in the wild even against well-funded companies with excellent security staff." The lesson is not "MFA is useless" — credential-driven attacks remain dramatically more common than these bypasses, and any MFA blocks the vast majority of them — but rather "the phishing-resistant tier exists for good reasons, and account recovery deserves the same scrutiny as login." For breach-side response when accounts have already been compromised, see Have I Been Pwned? What to Do If Your Email Was Leaked.
Authentication tier comparison and the long-term direction
Putting the pieces together, an honest tier comparison looks like this:
| Tier | Method | Factor type | Phishing-resistant? | Authoritative classification |
|---|---|---|---|---|
| 1 | Password only | Knowledge | No | Universally inadequate (DBIR 2025: stolen credentials in 22% of breach initial access) |
| 2 | SMS / voice OTP | K + Possession | No | NIST 800-63B-4: restricted authenticator; CISA: not phishing-resistant |
| 3 | TOTP authenticator app | K + Possession | No | NIST: AAL2-acceptable; CISA: not phishing-resistant |
| 4 | Push approval | K + Possession | Partial (with number matching) | NIST: AAL2 with mitigations; MFA fatigue risk |
| 5 | FIDO2 hardware key | K + Possession | Yes (domain bound) | NIST: AAL3-capable; CISA: recommended phishing-resistant |
| 6 | Passkey (synced WebAuthn) | Possession + Inherence | Yes (domain bound) | NCSC April 2026: first choice for consumers |
The NCSC announcement of April 23, 2026 is the most consequential single statement on consumer authentication in years. UK NCSC, on the CYBERUK Glasgow stage, formally recommended that "Passkeys should now be consumers' first choice of login across all digital services." The agency noted that passkeys are "at least as secure as, and generally more secure than" the strongest passwords paired with two-step verification, and cited that just over 50% of active Google services users in the UK now have a passkey registered. For services that do not yet support passkeys, NCSC's continued recommendation is "to use a password manager to create stronger passwords and keep using two-step verification."
Strictly, a passkey is a single-factor credential at the protocol level (the device unlocks via biometric or PIN, but the server sees one cryptographic credential). The security model is far stronger than a password, however, because the credential is domain-bound and cannot be relayed by a phishing page. The likely long-term direction is that "password plus 2FA" simplifies to "passkey" as service support broadens. The current state in mid-2026 is a coexistence period — passkey-supporting services let users set up passkeys, while older or transitional services still rely on password-plus-2FA.
If you'd like to generate strong, unique passwords for the services that do not yet support passkeys (and for the master account on a password manager), the Password Generator tool produces cryptographically secure random strings, supports passphrase mode, and runs entirely in your browser.
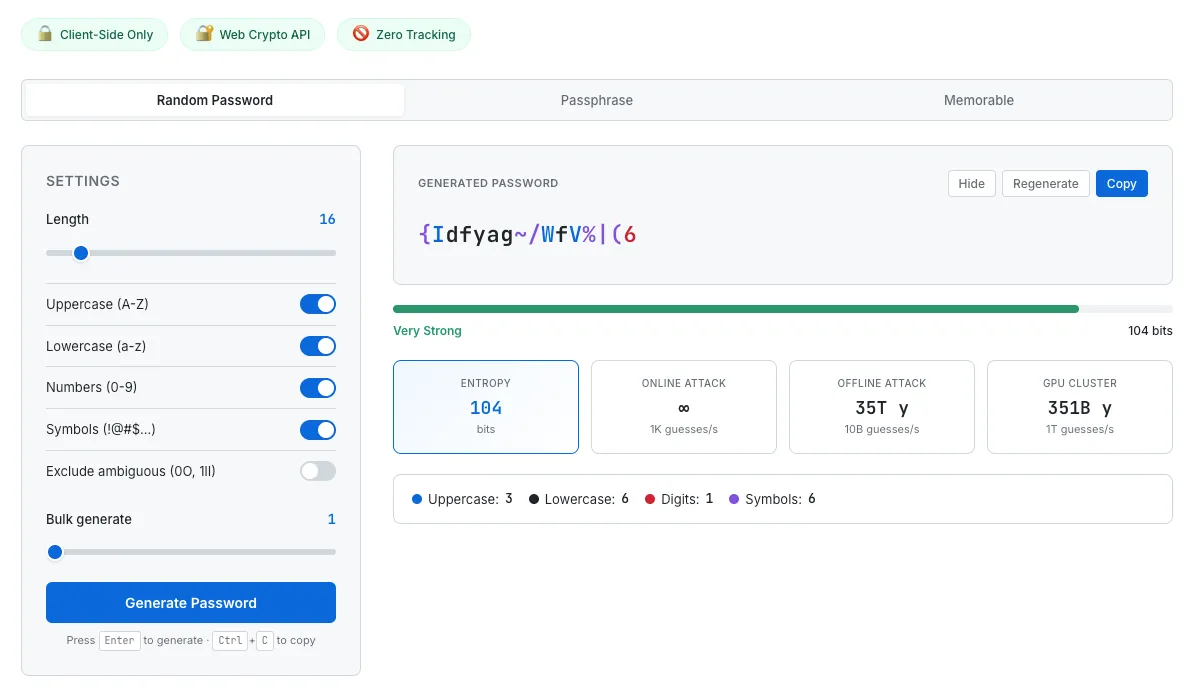
A strong, unique password is the knowledge factor in 2FA. The generator shows entropy and estimated crack times so the password's actual strength is visible, not just assumed.
Common questions about 2FA
What is two-factor authentication, in one sentence?
Combining two authentication elements from different categories — knowledge (password), possession (phone, security key), or inherence (fingerprint, face) — so that a leaked password alone cannot grant access.
Is SMS 2FA still safe to use?
NIST SP 800-63B-4 (July 2025) classifies SMS-based one-time passwords as a "restricted authenticator," meaning it is usable but with required mitigations because of SS7 attacks and SIM swap. CISA does not consider SMS phishing-resistant. SMS 2FA is meaningfully stronger than password-only and blocks essentially all automated credential attacks, but a TOTP authenticator app or FIDO2 hardware key is a stronger choice when both are available.
Are passkeys the same as 2FA?
Passkeys are not technically 2FA — they are a different credential model that often replaces both the password and the second factor with a single cryptographic credential bound to a domain. The user unlocks the passkey on the device with biometrics or a PIN. The security properties are at least as strong as a strong password plus 2FA, per NCSC's April 2026 assessment, and stronger against phishing. In practice, services that support passkeys typically let the user set up a passkey and keep their password as a fallback.
What is phishing-resistant MFA?
CISA defines phishing-resistant MFA as authentication that cannot be bypassed by an attacker tricking the user into entering credentials on a fraudulent site. The only widely available phishing-resistant option, per CISA, is FIDO2 / WebAuthn (security keys and passkeys). PIV/CAC smart cards qualify in government use. SMS, voice OTP, email OTP, and TOTP authenticator apps are not phishing-resistant by this definition because each can be relayed in real time by an Adversary-in-the-Middle proxy.
Why is hardware security key better than an authenticator app?
The authenticator app produces a 6-digit code that the user types into the website. If the user is on a fraudulent site, the attacker captures that code along with the password and uses both immediately. A hardware security key uses public-key cryptography and refuses to sign for the wrong domain — there is no copyable secret to phish. Google's internal data after replacing Authenticator with security keys for 85,000+ employees was zero account takeovers reported.
Can MFA be bypassed?
Yes, in specific ways. MFA fatigue (push-bombing) like the 2022 Uber breach. Real-time phishing proxies (evilginx2, EvilProxy) that defeat TOTP and SMS. Session-token theft after authentication. OAuth consent phishing. Weak account-recovery flows. FIDO2 is structurally resistant to the real-time phishing category specifically; the others apply across MFA types and benefit from layered defenses (endpoint hygiene, hardware keys, recovery flow scrutiny).
What 2FA should I use on my email?
For email — the master "reset everything" account — the published guidance points to the strongest available tier the service supports. Most major email providers (Gmail, Outlook, iCloud, ProtonMail) support hardware security keys and passkeys; many also support TOTP. Configuring a backup factor (a second key, backup codes printed and stored offline) is consistently recommended to avoid lockout.
This guide summarizes published guidance from NIST, CISA, NCSC, IETF, W3C, FIDO Alliance, Microsoft, Google, and incident reports as of May 2026. Authentication standards evolve — NIST SP 800-63B has had multiple revisions, NCSC's April 2026 passkey announcement is recent, and vendor support for passkeys is changing rapidly. Authenticator-tier comparisons describe general security properties, not personalized recommendations. Individual choices depend on service support, accessibility needs, and threat model. None of this is security advice or a substitute for professional consultation. For high-stakes account-protection decisions, please consult a qualified security professional.